CISA Urges Firms To Secure Microsoft Intune After Wipe Attacks
The Cybersecurity and Infrastructure Security Agency is urging organizations to secure Microsoft Intune environments after a cyberattack on medical technology company Stryker led to a mass wiping of devices, according to recent reports.
CISA’s advisory focuses on defensive steps for companies that use Microsoft Intune, a cloud-based service commonly used by enterprises to manage and enforce security policies on phones, laptops, and other endpoints. The alert follows an incident involving Stryker in which attackers were able to wipe large numbers of devices.
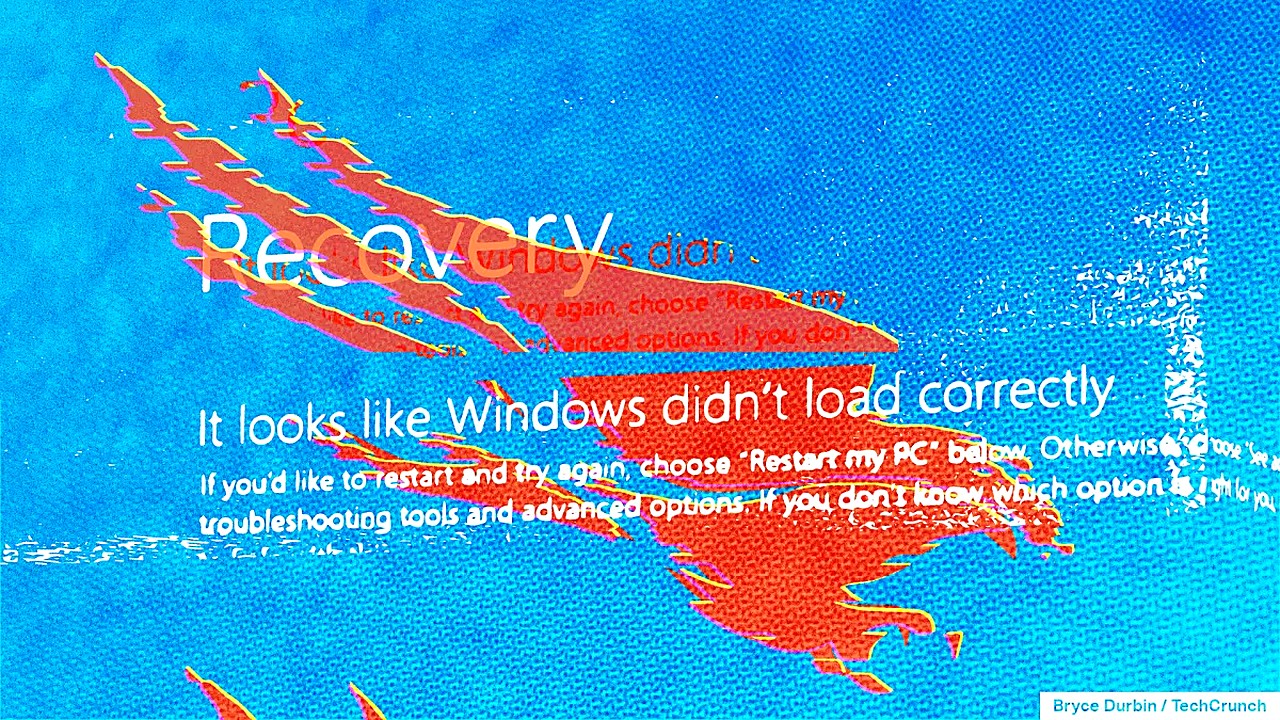
The attack on Stryker involved the remote wiping of tens of thousands of devices, as reported in recent coverage. The reports described the incident as notable for the scale of disruption and for the fact that the device resets could be carried out without deploying malware, underscoring how administrative tools can be abused when access controls fail.
The key issue for many organizations is that Intune and similar management platforms sit at the center of device security and operations. If a threat actor gains sufficient access, they may be able to lock out users, enforce new policies, or wipe devices at speed across an entire fleet. That can interrupt business operations quickly, complicate incident response, and raise costs as companies scramble to restore systems and redeploy hardware.
This development matters because device-management platforms are widely deployed across industries, including healthcare, where downtime can cascade into broader operational impacts. A large-scale wipe can disrupt communications and workflows even if data theft is not involved, and it can force organizations into time-consuming recovery processes such as re-enrollment of devices, reconfiguration of security settings, and verification that administrative access is restored to trusted personnel.
CISA’s warning is a reminder that securing a device-management plane is not solely an IT housekeeping task but a core resilience issue. Organizations that rely on centralized management tools may need to review who has administrative privileges, how those privileges are granted and audited, and what safeguards exist to prevent a single compromised account from triggering destructive actions across many endpoints.
In the near term, companies running Microsoft Intune can expect security teams to revisit their configurations and administrative access policies in light of the federal alert. Many organizations will also evaluate their ability to detect and respond to unauthorized changes within management consoles and confirm they can rapidly recover endpoints if a wipe or lockout occurs.
CISA’s advisory places fresh attention on the risks of attackers using legitimate management features for disruptive ends, and it adds urgency for enterprises to ensure that their Intune environments are locked down before a similar incident hits them.